VPS Proof of Concept for Docker and Traefik
This is a proof of concept for a VPS that includes ConfigServer Firewall (csf), Docker, Open SSH Server and Traefik as a reverse proxy to host multiple applications on the same Docker host.
The following notes document my experience while creating and configuring the VPS proof of concept local Virtual Machine with Ubuntu Server 16.04 on a Windows 10 host.
Virtual Machine
Since I am on my Windows 10 laptop for this, I used Hyper-V, an optional feature of Windows 10 Enterprise, Professional, or Education versions. Visit Install Hyper-V on Windows 10 | Microsoft Docs for more information on how to enable it. Virtual Machine creation from an iso image is fairly straight forward. More info at Create a Virtual Machine with Hyper-V | Microsoft Docs.
For installation, I downloaded the 64-bit Ubuntu Server 16.04.3 LTS (ubuntu-16.04.3-server-amd64.iso) bootable image from ubuntu.com/download/server.
Docker requires a 64-bit installation with version 3.10 or higher of the Linux kernel.
Create a Virtual Switch
Open Hyper-V Manger and select Virtual Switch Manager, and from there, select Create a Virtual Switch. For example, Name: WiFi Virtual Switch
Connection type: External Network Killer Wireless n/a/ac 1535 Wireless Network Adapter
With Hyper-V, To get external internet/network access with your VM, you need to create an External Virtual Switch. This will use your networks DHCP server, bridge mode if you will.
SSH Server
Install and configure OpenSSH. Once OpenSSH is installed, the virtual machine can be run headless and administered using secure shell (ssh) just as we would a VPS.
For a VPS, it is recommended that a non-root user with sudo privileges is used instead of root. Therefore, create a new user and add them to the sudo group. Instructions are available in the sudo section on my Linux page. After that’s done, disallow root password login.
ufw instead of csf
The default firewall configuration tool for Ubuntu is ufw. To use ufw instead of ConfigServer Firewall, configure and enable ufw prior to installing Docker. For example:
# allow incoming port 22
ufw allow ssh
# allow incoming ports
ufw allow 80
ufw allow 443
# turn it on
ufw enable
# verify
ufw status verbose
To Action From
-- ------ ----
22 ALLOW IN Anywhere
80 ALLOW IN Anywhere
443 ALLOW IN Anywhere
22 (v6) ALLOW IN Anywhere (v6)
80 (v6) ALLOW IN Anywhere (v6)
443 (v6) ALLOW IN Anywhere (v6)
Docker
To install the latest version of Docker, add the GPG key for the official Docker Ubuntu repository as a trusted APT repository key.
curl -fsSL https://download.docker.com/linux/ubuntu/gpg | sudo apt-key add -
Add the Docker repository to APT sources and update the package database.
sudo add-apt-repository "deb [arch=amd64] https://download.docker.com/linux/ubuntu $(lsb_release -cs) stable"
sudo apt-get update
Ensure that APT pulls from the correct repository.
apt-cache policy docker-ce
Install the latest version of Docker CE.
sudo apt-get install -y docker-ce
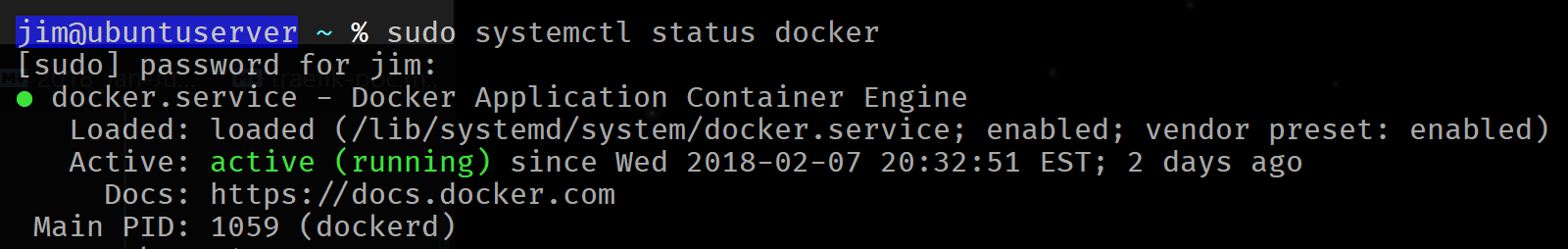
Docker should now be installed, the daemon started, and the process enabled to start on boot. Check that it’s running.
sudo systemctl status docker
Docker Compose
To get the latest release, install Docker Compose from Docker’s GitHub repository. Visit https://github.com/docker/compose/releases to lookup the version number. Then use curl to output the download to /usr/local/bin/docker-compose. For example,
# check current release, update as needed
sudo curl -L https://github.com/docker/compose/releases/download/1.19.0/docker-compose-`uname -s`-`uname -m` -o /usr/local/bin/docker-compose
# make executable
sudo chmod +x /usr/local/bin/docker-compose
# verify installation
docker-compose --version
Config Server Firewall (CSF)
Config Server Firewall contains a straight forward easy to understand configuration file. CSF also comes with a Login Failure Daemon that will alert you of large scale login attempts on ssh, mail and other servers. CSF also allows you to whitelist or blacklist IP addresses aside from the LFD real time monitoring and automatic IP blocking.
Disable the default firewall service.
sudo ufw disable
Since CSF is currently not available in the Ubuntu repositories, download it from the ConfigServer’s website into the home directory.
cd ~/
wget http://download.configserver.com/csf.tgz
Unpack the downloaded TAR archive.
tar -xvzf csf.tgz
Run the install script.
cd csf
sudo bash install.sh
Verify the installation,
sudo perl /usr/local/csf/bin/csftest.pl
If everything is fine, you should see the following output.
Testing ip_tables/iptable_filter...OK
Testing ipt_LOG...OK
Testing ipt_multiport/xt_multiport...OK
Testing ipt_REJECT...OK
Testing ipt_state/xt_state...OK
Testing ipt_limit/xt_limit...OK
Testing ipt_recent...OK
Testing xt_connlimit...OK
Testing ipt_owner/xt_owner...OK
Testing iptable_nat/ipt_REDIRECT...OK
Testing iptable_nat/ipt_DNAT...OK
RESULT: csf should function on this server
Optional cleanup: remove unpacked TAR files after the install has been verified.
cd ../
rm -rf csf
The next page covers CSF Docker configuration, basic auth for port specific password protection and Traefik Docker configuration.
